Using Google SSO With argoCD

At $DAYJOB I’ve been setting up an argoCD instance to build the continuous deployment pipeline and so far it’s been pretty slick.
However, the documentation only has example for github connection and Azure AD. Since my setup uses Gsuite I wanted to plug my authentication onto it.
argoCD has a nice way to handle this : they embed a dex server and this one can be configured using a ConfigMap. Let’s see this
Creating a Oauth2 client on Google
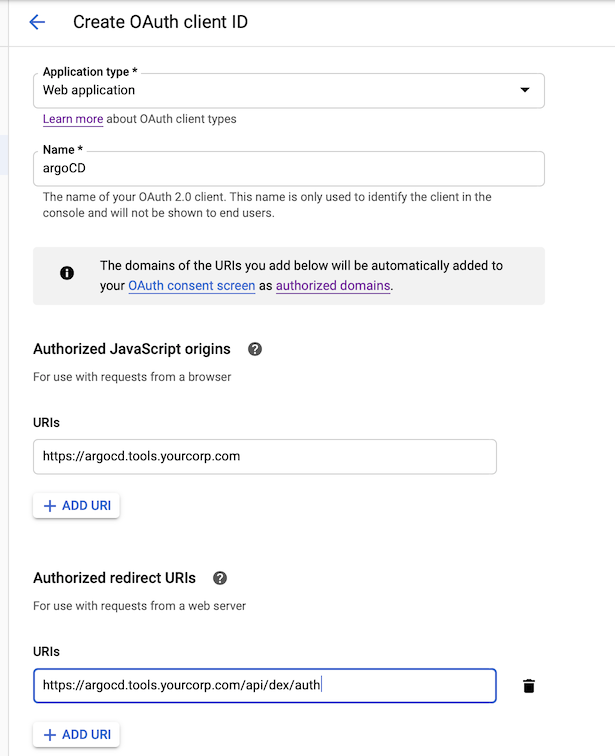
In your console, go to to the “API & services”, credentials sub menu and create a new Oauth2 client ID. Fill in the fields as follows :
You can then reuse the generated client ID and secret in the configmap as is :
kubectl -n argocd edit configmaps argocd-cm (if you used the argocd namespace)
apiVersion: v1
data:
dex.config: |
connectors:
- config:
issuer: https://accounts.google.com
clientID: "YOUR_CLIENT_ID"
clientSecret: "YOUR_CLIENT_SECRET"
type: oidc
id: google
name: Google
url: https://argocd.tools.yourcorp.com
You will now have a nice “LOGIN WITH GOOGLE” button on the login screen.
But we’re not done yet, since we need to create policies for our users. They are located in the argocd-rabc-cm configmap.
apiVersion: v1
data:
policy.csv: |
# Role definition : these users are admin
g, you@yourcorp, role:admin
g, colleague@yourcorp.com, role:admin
# policies : can be done multiple times to give access to multiple projects
# See https://github.com/argoproj/argo-cd/blob/master/docs/operator-manual/rbac.md for more information
p, dev1@yourcorp.com, applications, *, project1/*, allow
p, dev2@yourcorp.com, applications, *, project2/*, allow
# default policy for people logging in --> no privileges, they are blind and can't do anything
policy.default: ""
scopes: '[email, group]'
Here project1 and project2 are argoCD projects, as defined in the configuration. This allows to have a fined grained access and avoids cluttered dashboard for users.
Hope that helps
